It’s been a big month, with many new capabilities and features! You can now create Guardrails to control costs by monitoring pull requests and triggering actions when thresholds are exceeded. You can also use cost policies to scan your code repos for money saving opportunities (e.g. change gp2 to gp3 volume types) and create tasks to help engineering teams take action.
There’s also Jira integration, README badges, custom reports, the ability to override the cloud region and lots of new resources.
Upgrade to version v0.10.15 and log in to Infracost Cloud to see the new features.
Guardrails
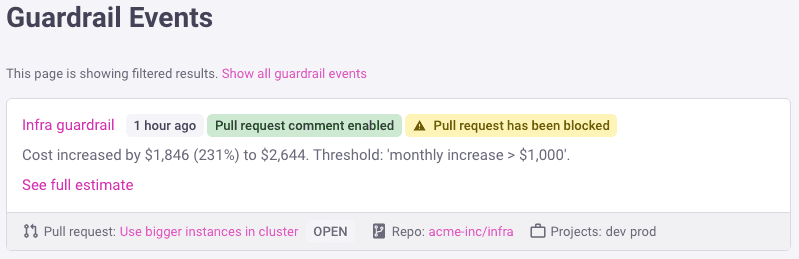
Guardrails help you control costs by monitoring pull requests and triggering actions when your defined thresholds are exceeded. Two common use-cases are monitoring pull requests for:
The monthly budget being exceeded, e.g. notify the budget holder if a pull request for their repo results in the monthly cost of the whole repo to go above $30K/month.
Unexpected cost spikes, either by defining a fixed threshold or percentage, e.g. notify the FinOps team when a pull request into production environments increases the costs by more than 10%.
Once you define a cost or percentage based threshold for the relevant repos, projects, and branches, you can specify what action should be taken. Action can be to email certain people or sending a Slack notification; leaving a custom comment in the pull request so the engineer is aware that they have exceeded the threshold; or even blocking pull requests. See the guardrail docs on how to use this feature.
From Infracost Cloud you can see all your Guardrails in a central place, and also an audit trail of when they have been triggered:
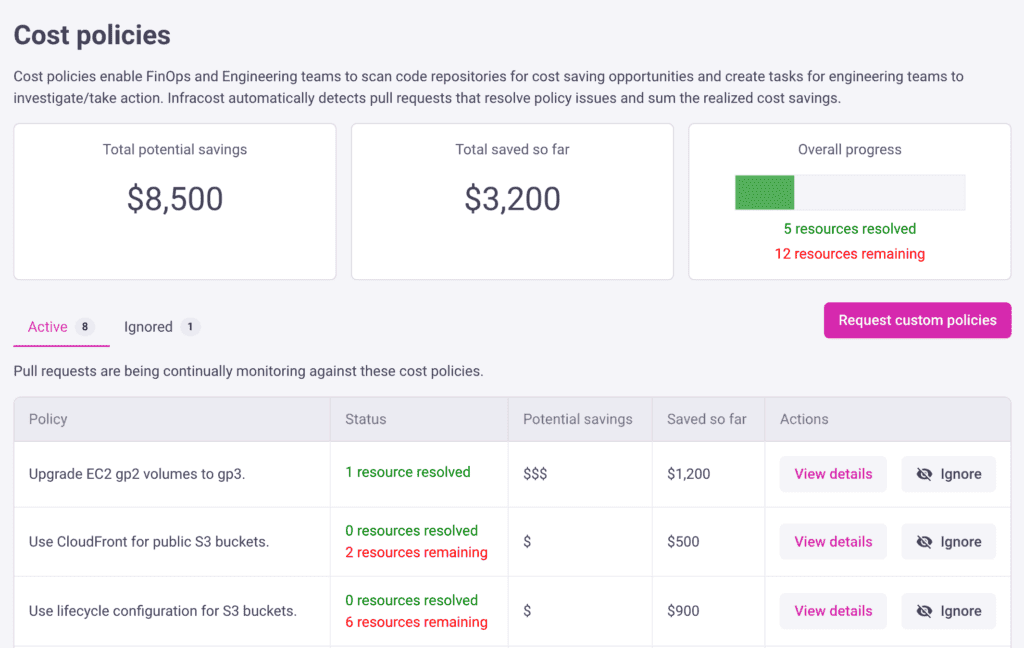
Centralized cost policies
With cost policies you’ll be able to define central policies and scan your repositories for cost saving opportunities. You can also see which repositories are not following your policies and create tasks to help engineering teams take action. The policies are checked and tracked each time a pull request is sent.
Policies can be created for any infrastructure-as-code attributes for AWS, Azure and Google. Some example AWS policies that we’ve created are: upgrade EC2 gp2 volumes to gp3, use CloudFront for public S3 buckets, add autoscaling for DynamoDB RCUs, and use S3 for VPC flow logs.
We are releasing Cost policies with a number of pre-defined policies. We’d love to work with you to define your own custom policies, or make a bigger library of policies to be used by the community. Please reach out to my co-founder, Hassan, on hassan.hosseini@infracost.io to learn more about custom policies.
This feature would not have been possible without the amazing work of the Open Policy Agent folks, as the Rego language is used behind the scenes.
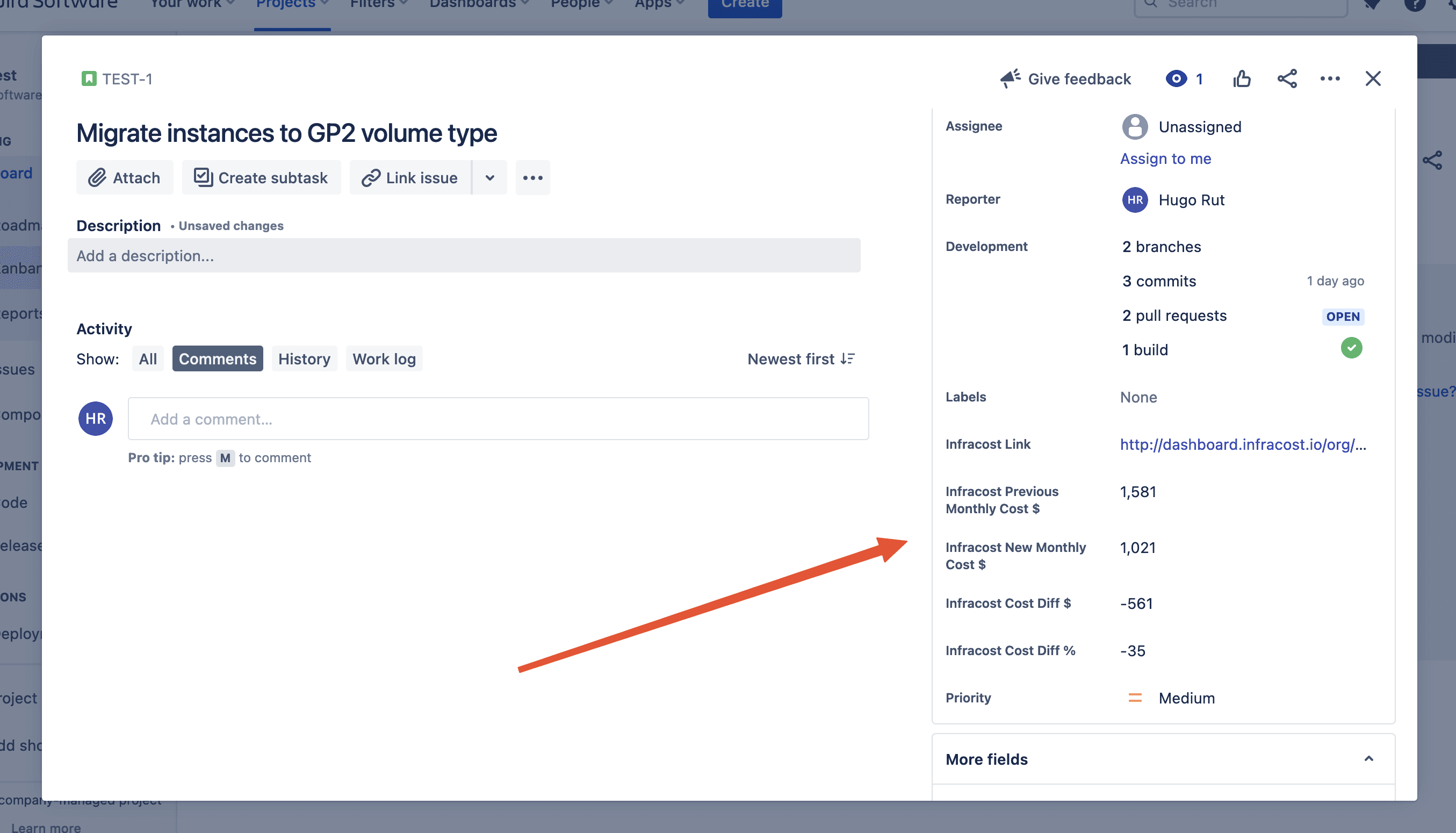
Jira integration
One of the reasons Infracost CI/CD is loved by engineers is that it sits directly in their workflow. They don’t need to do anything different, they keep shipping code and Infracost meets them where they are and helps them. When we are talking to engineering managers and team leads, they don’t deal with pull requests but with Jira issues, and product releases. The Jira issues contain the reason why the code is changing, and GitHub contains what is being changed.
That’s why I’m super excited about this feature. You can now connect Infracost and Jira together. Cost estimates are sent directly into Jira issues so you can track the most impactful tickets your team is working on as it relates to the cloud bill. Infracost creates custom fields in Jira with the cost estimate, so you can use those fields in Jira reports as well Jira’s workflow engine. If a Jira issues contains multiple pull requests, Infracost automatically detects this and sums up costs and inputs them directly into Jira. To get started, check out the Jira integration docs.
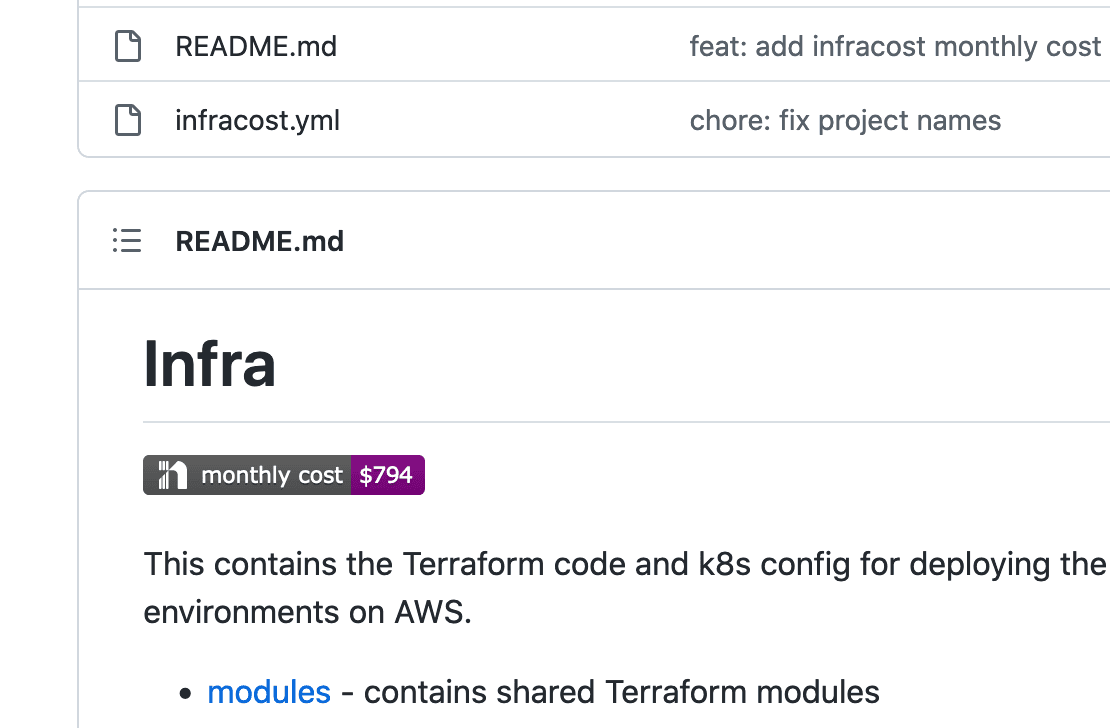
README badge
Add a cost badge in your repository README.md files to enable engineers to see the repo’s latest cost estimate quickly. This is specially useful for Terraform module repos where a central platform team creates re-usable modules for development teams, who are often unaware of the costs of those modules.
Override cloud region
There can be a big difference in costs between cloud regions so it can be useful to get a quick cost estimate of using a different region before infra any code is changed. The following new environment variables can be used to override the region when using the infracost breakdown and diff commands:
INFRACOST_AWS_OVERRIDE_REGIONfor AWSINFRACOST_AZURE_OVERRIDE_REGIONfor AzureINFRACOST_GOOGLE_OVERRIDE_REGIONfor Google
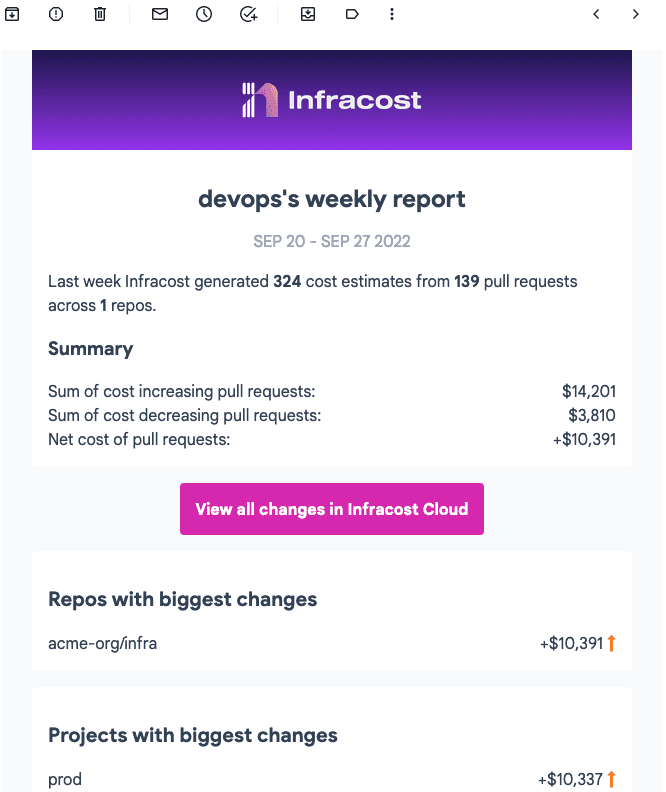
Reports
The new reports page enables you to create daily/weekly/monthly reports and get a summary of the most impactful cost changes across all repos. When creating a report, you can also filter on specific pull requests to be included in the report, e.g. only report on certain repositories or merged pull requests.
New resources
We added support for the following cloud resources and also added support for the new AWS regions eu-central-2, eu-south-2 and ap-south-2:
Google Compute custom machine types
Azure Attestation Provider
azurerm_attestation_providerAWS FSx OpenZFS File System (aws_fsx_openzfs_file_system), Lambda tiered pricing and EC2 host
aws_ec2_host
Other improvements
We also released a few other improvements:
Infracost can be used with CDK for Terraform.
Add cache for Terragrunt source files. Significantly speeding up Terragrunt HCL evaluation by caching already downloaded modules and copying them to a destination if they are included again.
The
infracost breakdownanddiffcommands have a new--include-all-pathsthat sets the project auto-detection to use all subdirectories in given path. Together with the existing--exclude-pathflag this enables you to control how Infracost is run in your repository directories. These options are also available in the config-file:version: 0.1
projects:
- path: code
include_all_paths: true
exclude_paths:
- "modules/**"The
infracost commentcommand has a new--show-all-projectsflag that shows all projects in the table of the comment output. This is useful if you want to see project breakdown costs even if those projects have not changed.The GitHub App integration shows you who approved pull requests, who merged pull requested and any labels that the pull request had. This additional context is useful when debugging cost spikes and is available in the Infracost Cloud dashboard as well as the CSV export.
There is a new version of the VSCode extension with improved error handling, bug fixes and simpler onboarding flow.
The Terraform Enterprise Run Task integration docs have been updated to include details of the firewall configurationsyou need to make.
Community content
Many thanks to first time contributors @peterdeme, @yogeshCt3 and @7onn. Also shout-out to the following people for sharing their knowledge with the rest of the community:
Wenqi Glantz: Infracost + Terraform + GitHub Actions = Automate Cloud Cost Management
Tobias Mueckl: Cloud-Kosten im Blick behalten mit Infracost für Terraform
Antonio Carlos da Silva Junior: Utilizando Infracost para estimar custos no Azure com Terraform
Mauricio Pinheiro Gomes: talked about Infracost at DevOps Days Rio de Janeiro
👉 Finally, as a thank you to our open-source community, and to celebrate the end of the year, we are reducing the price of Infracost Cloud from $50 per seat per month to $30 per seat per month. This offer is live now, and ends on the 31st December 2022!
Infracost ROI Report
Learn how the ROI of shifting FinOps left is measured


