Cloud Security Policies: Shift-Left Security for Your Infrastructure Code
Most security scanners treat infrastructure-as-code like any other codebase: pattern matching, regex rules, surface-level checks. But infrastructure code isn’t like application code. Variables reference other variables. Modules pull in external dependencies. A single Terraform code block might expand into dozens of cloud resources, after evaluation, across different environments.
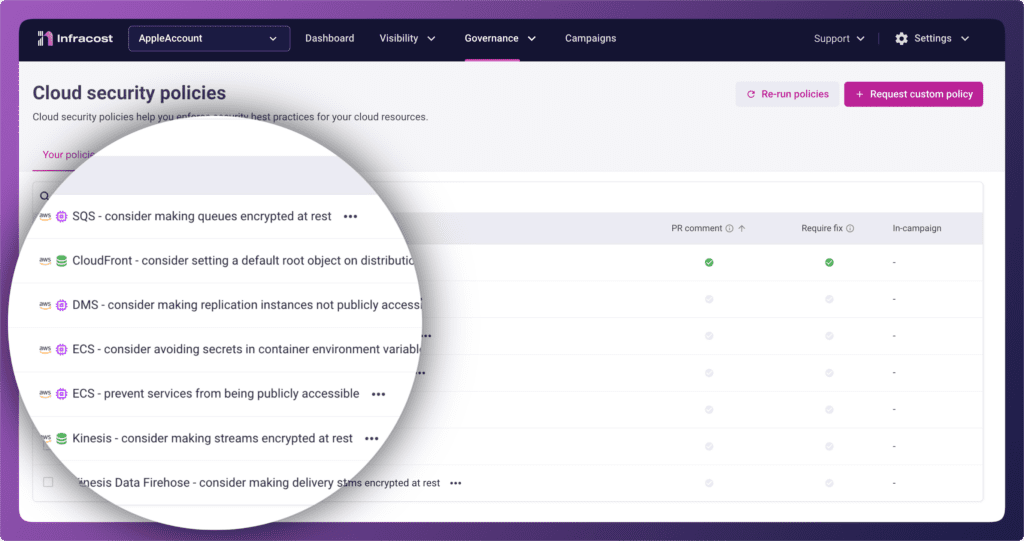
We’ve spent years building deep parsing for Terraform, CloudFormation, and AWS CDK. We evaluate variables, load external modules, and understand what your infrastructure will actually become… not just what the text looks like. That foundation now powers a new category of governance: Cloud Security Policies.
Why security in Infracost?
The path here was customer-driven. We started with FinOps policies to catch cost issues before deployment. Then enterprise customers asked us to check tagging because FinOps teams rely heavily on consistent tags for cost allocation. Then came the recurring question: “Can you also scan for security issues?”
Specifically, customers wanted cloud security posture management (CSPM) checks, for example AWS Security Hub standards and Azure best practices, but applied at the infrastructure-as-code layer, before misconfigured resources ever reach production.
So we built it.
The right people, the right info, the right time, the right place
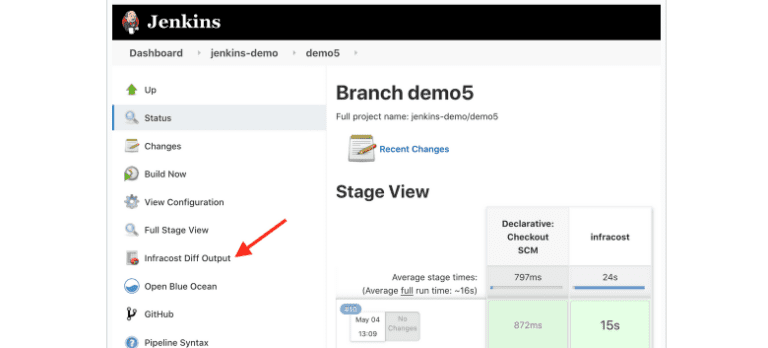
Enterprise customers love the developer experience Infracost provides. Connect your GitHub, GitLab, or Azure Repos organization and we automatically detect every infrastructure-as-code repository. No manual configuration per repo. No yaml files to maintain. Your developers get superpowers within the source control systems they already use.
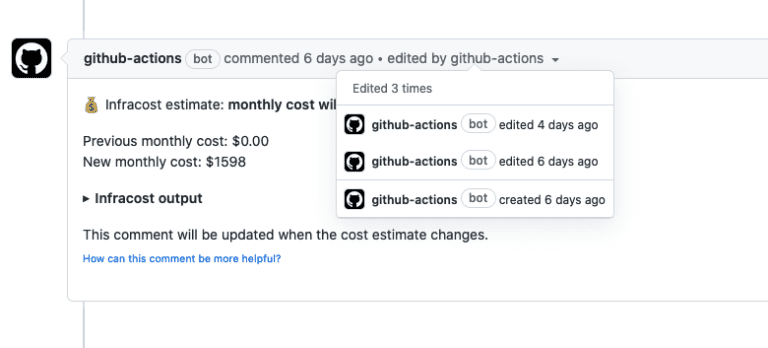
That last part matters. Developers never leave their workflow. They don’t log into another dashboard, learn another tool, or check a separate system. Security issues appear directly in pull requests. Exactly where the engineer who can fix them is already working.
This is what shift-left actually looks like: the right information reaching the right people at the right time, in the right place.
Prevention, remediation, and everything in between
Pull request comments focus on prevention. When a CloudFront distribution is missing WAF protection or an RDS instance lacks encryption at rest, the developer sees the issue before merge. Not in a security report weeks later.
AutoFix pull requests tackle existing issues. Rather than creating tickets that sit in a backlog, Infracost generates ready-to-merge fixes that engineers can review and apply.
Bot commands keep developers in flow. Dismiss or snooze issues directly from pull request comments using @infracostcommands. Security and platform teams maintain oversight while developers retain agency.
Campaigns: direct efforts, track progress
All of this is powered by Campaigns.
For cloud security practitioners and engineering leadership, Campaigns provide the control plane for governance across the enterprise. Create a campaign, assign the policies that matter, target the repositories that need attention, and track progress with the metrics that matter:
- % of new issues prevented: How effectively are you stopping problems before they reach production?
- % of existing issues fixed: How quickly is your backlog shrinking?
Campaigns transform security governance from “we have policies” to “we’re measurably improving.” Leadership gets visibility into remediation velocity. Platform teams can direct engineering efforts strategically. And developers get clear, actionable guidance rather than overwhelming backlogs.
Launch policies
We’re launching with 22 policies covering critical security configurations across AWS and Azure:
| Cloud | Service | Policies |
|---|---|---|
| AWS | SQS | consider making queues encrypted at rest |
| AWS | CloudFront | consider setting a default root object on distributions |
| AWS | DMS | consider making replication instances not publicly accessible |
| AWS | ECS | consider avoiding secrets in container environment variables |
| AWS | ECS | prevent services from being publicly accessible |
| AWS | Kinesis | consider making streams encrypted at rest |
| AWS | Kinesis Data Firehouse | consider making delivery streams encrypted at rest |
| AWS | DMS | endpoints should use SSL |
| AWS | EC2 | Amazon EC2 and launch templates should not associate a public IPv4 address |
| AWS | RDS | DB instances should have encryption at-rest enabled |
| AWS | CloudFront | distributions should have WAF enabled |
| AWS | EC2 | consider disabling associate public IP address in launch templatesActive policy |
| AWS | EC2 | require Instance Metadata Service Version 2 (IMDSv2) |
| AWS | KMS | consider enabling automatic key rotation |
| AWS | RDS | consider enabling CloudWatch log exports |
| AWS | RDS | should copy tags to snapshots |
| AWS | S3 | consider blocking public access for the S3 access points |
| AWS | EC2 | VPC default security groups should not allow inbound or outbound traffic |
| AWS | ELB | Application Load Balancer should be configured to redirect all HTTP requests to HTTPS |
| Azure | App Service | consider enabling HTTPS-only mode |
| Azure | App Service | consider using latest TLS version |
| Azure | Storage Account | consider disabling public network access |
Each policy can be customized with Risk, Effort, and Deployment metadata, the same framework our enterprise customers use for FinOps policies to help teams prioritize remediation based on organizational context.
What makes this different
Generic security scanners don’t understand infrastructure as code the way Infracost does. They see text; we see infrastructure.
Other tools require manual repo configuration, separate dashboards, and context-switching that breaks developer flow. Infracost meets developers where they are: in their pull requests, in their existing workflow, with automatic detection across every IaC repository in their organization.
Get started
Already using Infracost Cloud?
Cloud security policies are available now. Navigate to Governance → Cloud security policies to enable the policies relevant to your organization. Policies will begin evaluating on your next pull request.
New to Infracost?
Sign up for Infracost Cloud—it’s free to get started. Connect your version control provider, and you’ll have cost visibility, FinOps policies, and cloud security policies working across your infrastructure repositories in minutes.
What’s next
This launch covers AWS and Azure services aligned with security hub standards and cloud best practices. We’re expanding coverage based on customer feedback and if there’s a security control you need, let us know.
Join our community Slack and tell us what you’d like to see next.