April 2023: Unblock Guardrail Pull Requests, Dynamic Config Files & Many New Resources!
The all-new Infracost Guardrails now enable you to approve and unblock pull requests (PRs) that were blocked by the budget guardrail. This month’s release includes dynamic and org-level config files, which will help with repos that have multiple Terraform projects (e.g. mono repos or teragrunt repos). We have also added support for more AWS and Azure resources, taking our total coverage to over 1,000 Terraform resources! Additionally, you can now set the PR status for GitLab & Azure Repos to merged, and view PR histories in Infracost Cloud.
Log in to Infracost Cloud or upgrade to CLI version v0.10.19 to use the new features.
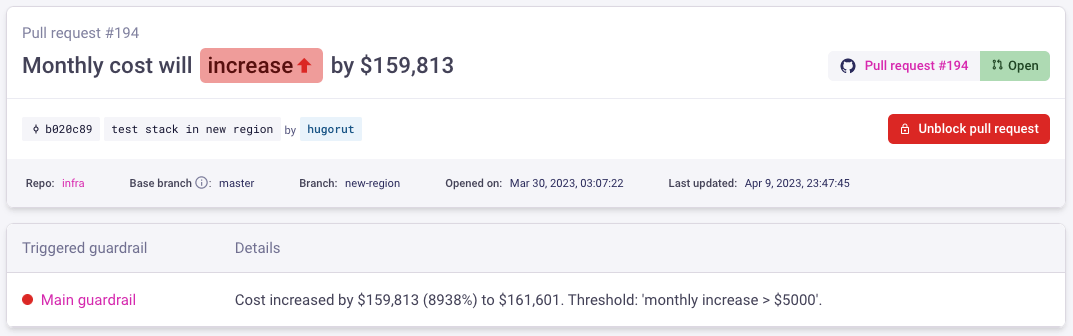
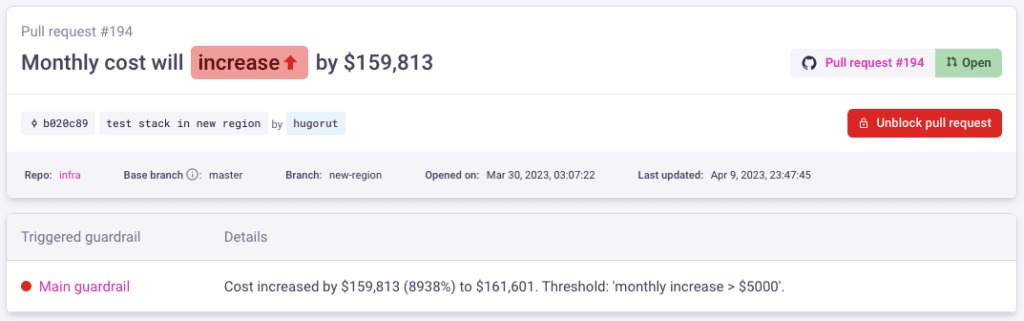
Guardrails: unblock pull requests
Guardrails help you control costs by monitoring pull requests (PRs) and triggering actions when your defined thresholds are exceeded. Once you define a cost or percentage-based threshold for the relevant repositories, projects, and branches, you can set up email, Slack, or Microsoft Teams notifications. You can also customize the PR comment (e.g. “This change exceeds the budget, please discuss with your team lead”) or even block the PR until it has been reviewed.
When a pull request (PR) is blocked by a guardrail, the email notification will now include a link to the PR page in Infracost Cloud. From there (as shown below), you can review the cost estimate, see details of the triggered guardrail, and unblock the PR. If someone with admin access on GitHub overrides the guardrail and merges the PR, Infracost Cloud will send an additional email notification to the people subscribed to the guardrail. This provides everyone with visibility of the change, thus preventing surprises in the cloud bill. To test this new feature, create a guardrail.
Dynamic config files
Config files specify how Infracost should run on a repository with multiple Terraform projects (e.g. infrastructure mono repos or terragrunt repos). The costs for those projects are combined into one pull request (PR) comment and shown together in Infracost Cloud.
Previously, you had to manually define projects in config files. This meant that when a project was added or removed from the repository, the config file had to be updated. This was cumbersome for repositories with many projects, and impossible to do efficiently with large enterprise repositories that had hundreds or thousands of projects.
Last month, we added support for dynamic config files using a new template syntax. This enables you to keep Infracost in sync with your repository’s changing projects, thus removing the need to maintain a hardcoded config file.
As shown below, the template file is used by the infracost generate command to generate a config file. The Infracost GitHub App also automatically detects this syntax in the infracost.yml or infracost.yml.tmpl repo root files and generates the config file. If you’re already familiar with Kubernetes Helm templates, you’ll find working with the syntax straightforward and intuitive. Checkout the docs to learn more.
- 1. Run CLI command
- 2. Example input config file template
- 3. Example output config file
infracost generate config --repo-path=. \
--template-path=infracost.yml.tmpl \
--out-file=infracost.yml
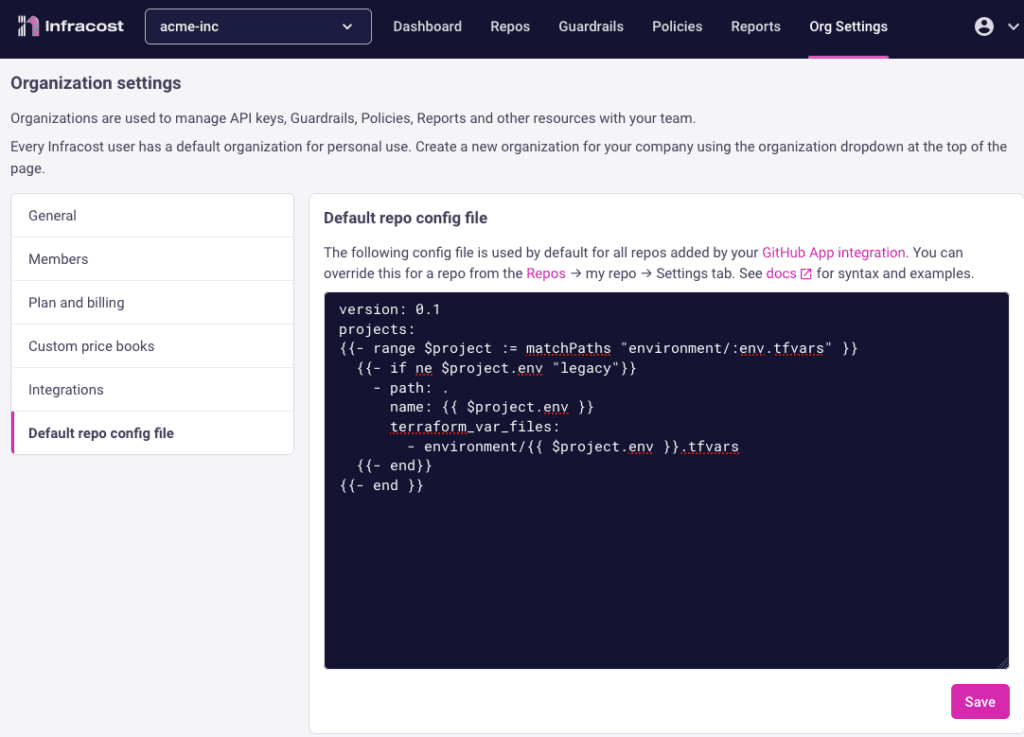
infracost breakdown --config-file=infracost.ymlDefault organization config file
Enterprises often have hundreds of infrastructure code repositories, most of which follow a similar directory structure. Infracost GitHub App users can now define a default config file in Infracost Cloud to be used by all of their repositories. This config file can be overridden on a per-repo basis from the Repos > my-repo > Settings page, or by adding an infracost.yml to the repo root. This enables you to add many repositories to Infracost quickly 🚀
New resources
Last month we made a big push to add the following Azure resources. We now cover over 1,000 Terraform resources across AWS, Azure and Google 🚀 We also added support for AWS Spot instances.
- Azure App Service
- Azure Insights Standard Web
- Azure Linux and Windows Function Apps
- Azure Log Analytics Basic Logs Ingestion
- Azure Monitor Action Groups
- Azure Monitor Diagnostics Settings
- Azure Monitor Log Alerts (scheduled query rules alerts)
- Azure Monitor Metric Alerts
- Azure Monitor Data Collection Rules
- Azure Recovery Services and Azure Backup for an Azure VM
- Azure Storage costs for BlobStorage, StorageV1, QueueStorage & Storage File Shares
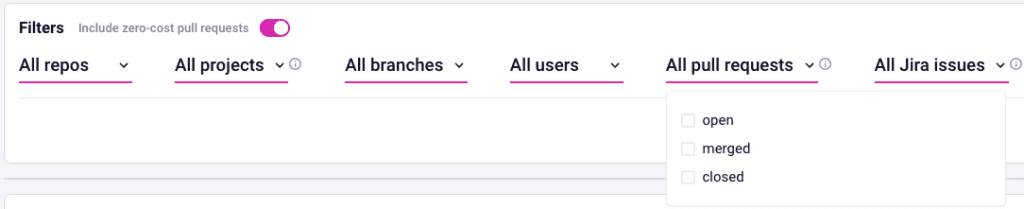
Pull request status for GitLab & Azure Repos
The PR status in Infracost Cloud lets you filter on PRs that are merged and have impacted your cloud bill, or are still open and can be reviewed. The PR status is also useful when setting up daily or weekly reports as you can review what has already been merged.
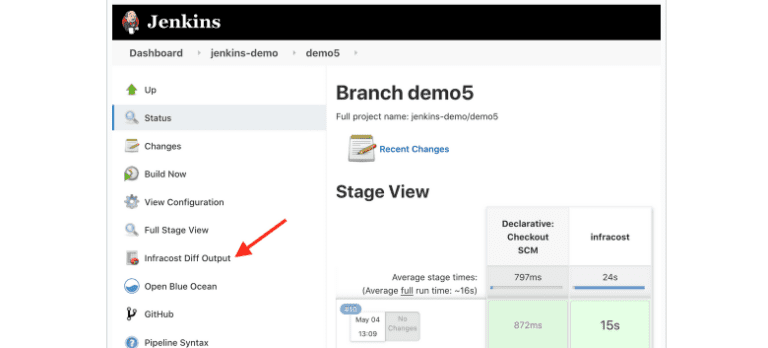
GitLab and Azure DevOps users can now update the PR status from their pipelines. The Infracost GitHub App integration shows this automatically.
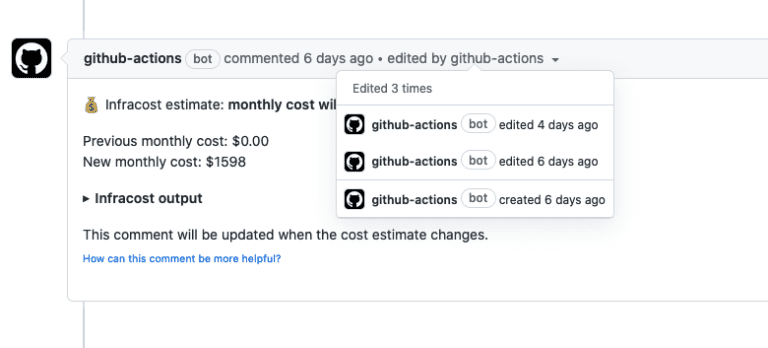
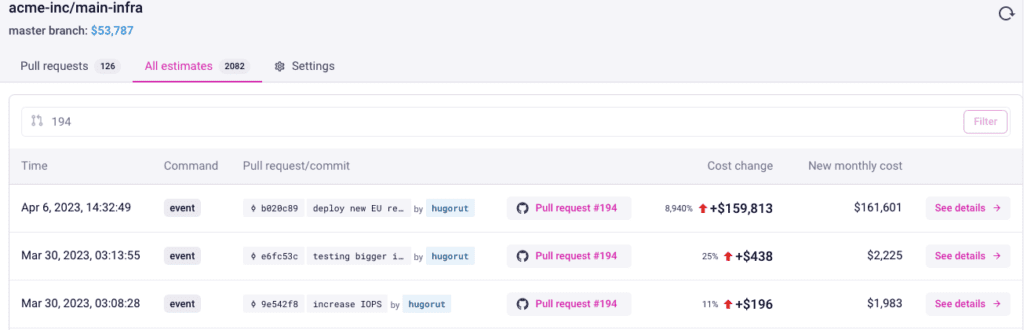
See pull request history
PRs often take several iterations of changes before they are merged. You can now see the history of PR costs in Infracost Cloud. This audit trail is specially useful when guardrails are used as it enables engineering management and FinOps teams to see how the PR costs were changed after a guardrail was triggered.
Community content
Many thanks to first time contributor @lucastercas – InfraSocks are coming your way! Also shout-out to the following people for sharing their knowledge with the rest of the community:
- Stacy Véronneau: YouTube demo of FinOps on GCP using Infracost
- Taufiqur Ashrafy: InRhythm Lightning Talk about Infracost (forward to 1h 20mins for the Infracost section)
- Fahd Mirza: FinOps: Infracost Terraform Tutorial
- Prayag Sangode: Infracost – Cloud Cost Estimate for Terraform
Finally, checkout our blog AWS cost calculator vs Infracost!